- Home
- /
- SAS Communities Library
- /
- Auditing authorization changes in SAS Viya
- RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
Auditing authorization changes in SAS Viya
- Article History
- RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
SAS Viya's Audit service provides administrators with the ability to understand how the platform is being used and what types of activities users are performing (or attempting). In addition to user activity auditing, Viya's auditing implementation also captures (and provides a way to query) information about events relating to security of your platform. In this post, we'll examine a specific example; querying audit data to glean information about changes to Custom Group membership and folder authorization.
Audit changes to group membership
Unfortunately, it is not uncommon for users of a software platform to be granted more access than necessary to perform their job. Many of us have seen first-hand the granting of excessive privileges as an easy-button solution to getting things done, particularly as project deadlines loom. How many times have you seen an administrator (or yourself) add a user (or yourself!) to the administrators or sudoers groups to bypass a permissions issue?
Source: xkcd.com
While it might seem a quick and easy solution, granting elevated privileges to just anyone is dangerous for obvious reasons. The Audit service can help track changes to group membership in Viya so that they can be corrected where necessary. It may also be a requirement to keep a record of changes to entitlements for regulatory reasons.
Let's walk through an example.
Suppose we, as the Viya administrator, have added a user, Fernanda, to the SAS Administrators custom group. This change to group membership results in the Audit service capturing an audit record, which we can query using the sas-viya CLI.
/opt/sas/viya/home/bin/sas-viya --output text audit list --sort-by ~timestamp --application identities
Note that we are filtering for records from the Identities service/application. The output of this command will show an audit record for the group membership change.
ID Time Stamp Action State User ID Application URI 16ffc0f2-4cd0-49d0-a53c-79cd2447e84d 2021-03-30T03:38:46.814Z create success geladm identities /identities/groups/SASAdministrators/userMembers/Fernanda
When a user is added to a custom group, the Audit service captures a record showing a create action was performed by the user making the change (geladm in this case) along with the timestamp. The group and the user being added to it are identifiable from the URI. Looking at the details of the record will tell us that the request to update the group membership was via a HTTP PUT request.
/opt/sas/viya/home/bin/sas-viya --output text audit show-info --id 16ffc0f2-4cd0-49d0-a53c-79cd2447e84d
ID 16ffc0f2-4cd0-49d0-a53c-79cd2447e84d Time Stamp 2021-03-30T03:38:46.814Z Type resource Action create State success User ID geladm Remote Address 127.0.0.1 Properties referringApplication : SASEnvironmentManager Application identities URI /identities/groups/SASAdministrators/userMembers/Fernanda HTTP Status Code 201 HTTP Method PUT
Conversely, when Fernanda is removed from the custom group, a similar record is created, this time showing a delete action was executed (via a HTTP DELETE).
/opt/sas/viya/home/bin/sas-viya --output text audit list --sort-by ~timestamp --application identities
ID Time Stamp Action State User ID Application URI dab82354-f8f8-4c1d-9a7c-5c81db252dc2 2021-03-30T03:45:38.604Z delete success geladm identities /identities/groups/SASAdministrators/userMembers/Fernanda 16ffc0f2-4cd0-49d0-a53c-79cd2447e84d 2021-03-30T03:38:46.814Z create success geladm identities /identities/groups/SASAdministrators/userMembers/Fernanda
Auditing changes to folder authorization
Now let's see what audit records are captured if we change folder authorizations. In this example, we have granted Fernanda read access to a Viya folder called gelcorp, which resides in the SAS Content root folder. Using the CLI, we can see that the audit data for this kind of change comes from the authorization application. (Note that adding the --details flag to the command will print "Authorization rule access" to the Description column for records representing changes to authorization rules - useful if not filtering the output by application.)
/opt/sas/viya/home/bin/sas-viya --output text audit list --sort-by ~timestamp --application authorization
ID Time Stamp Action State User ID Application URI a307eba0-c6e0-41b6-836f-5c4df7212328 2021-03-30T06:44:37.33Z create success sas.folders authorization 9a361788-8752-4ca4-b71b-b5ffa7568ae6 2021-03-30T06:43:35.019Z create success sas.authorization authorization
Let's look at these records in more detail.
The first (the bottom one) shows a successful create from the user sas.authorization. These types of records (from this internal user) represent changes to authorization.Use
sas-viya audit show-info
to view more information about the change.
/opt/sas/viya/home/bin/sas-viya --output text audit show-info --id 9a361788-8752-4ca4-b71b-b5ffa7568ae6
ID 9a361788-8752-4ca4-b71b-b5ffa7568ae6
Description Authorization rule access
Time Stamp 2021-03-30T06:43:35.019Z
Type security
Action create
State success
User ID sas.authorization
Properties containerUri :
id :
objectUri : /folders/folders/105bf2d8-65e3-4b85-8ad7-321e6f68d4ed/**
permissions : read
principal : Fernanda
principalType : user
type : GRANT
Application authorization
As evident in the output above, the record shows the timestamp, the objectUri, principal, permissions and type (GRANT or DENY). Very useful information for user access auditing.
So what is the other record that was displayed when we listed audit records from the authorization application (the top one, with a user-id of sas.folders)?
Let's run show-info again to find out.
/opt/sas/viya/home/bin/sas-viya --output text audit show-info --id a307eba0-c6e0-41b6-836f-5c4df7212328
ID a307eba0-c6e0-41b6-836f-5c4df7212328
Description Authorization rule access
Time Stamp 2021-03-30T06:44:37.33Z
Type security
Action create
State success
User ID sas.folders
Remote Address 10.42.4.65
Properties containerUri : /folders/folders/9b0afb0f-e7d2-4cff-baf6-6b6c1b207ba1
id :
objectUri : /folders/folders/9b0afb0f-e7d2-4cff-baf6-6b6c1b207ba1/**
permissions : add,remove,delete,read,secure,update
principal : Fernanda
principalType : user
type : GRANT
Application authorization
Interestingly, this rule appears to grant Fernanda full permissions to a folder. We can use the folder ID from the objectUri property to find out.
/opt/sas/viya/home/bin/sas-viya --output text folders show --id 9b0afb0f-e7d2-4cff-baf6-6b6c1b207ba1
Id 9b0afb0f-e7d2-4cff-baf6-6b6c1b207ba1
Name Fernanda
Description The user folder for Fernanda
Type userFolder
MemberCount 3
ParentFolderUri /folders/folders/88ec1ebe-91a6-427a-a8da-8417ff937891
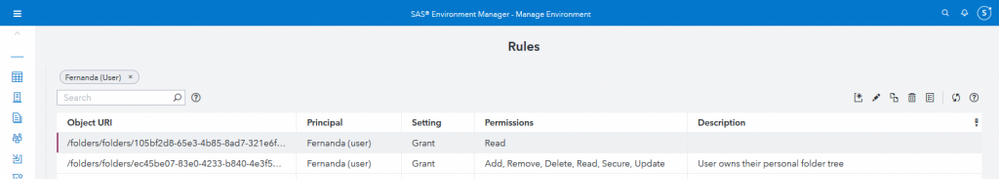
It's Fernanda's user folder. The rule is applied and the audit record created when the user logs in for the first time. As with other rules, folder authorization rules appear in the Rules page of SAS Environment Manager.
Select any image to see a larger version.
Mobile users: To view the images, select the "Full" version at the bottom of the page.
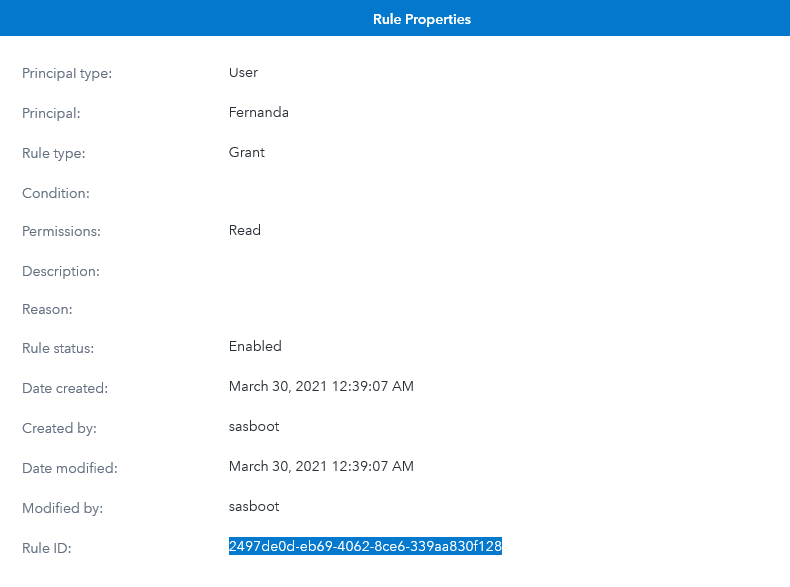
If we select the rule for the gelcorp folder, and then click the properties button, we can see the Rule ID. (We can also use the sas-viya CLI's authorization plugin to get this information.)
If we then remove Fernanda's access to the gelcorp folder, the Audit service captures a record with a delete action.
/opt/sas/viya/home/bin/sas-viya --output text audit list --sort-by ~timestamp --application authorization --type security --action delete
ID Time Stamp Action State User ID Application URI 1846bd39-270f-44ca-9cde-3c559bf451a6 2021-03-30T04:21:23.974Z delete success sas.authorization authorization
If we run audit show-info, we can see a reference to the Rule ID that was deleted in the Properties field.
/opt/sas/viya/home/bin/sas-viya --output text audit show-info --id 1846bd39-270f-44ca-9cde-3c559bf451a6
ID 1846bd39-270f-44ca-9cde-3c559bf451a6 Description Authorization rule access Time Stamp 2021-03-30T04:21:23.974Z Type security Action delete State success User ID sas.authorization Properties id : 2497de0d-eb69-4062-8ce6-339aa830f128 Application authorization
More information
Refer to the documentation for more information on auditing in SAS Viya.
Please leave a comment below to ask questions or share your own experiences. Thank you for reading!
Find more articles from SAS Global Enablement and Learning here.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hi @AjmalFarzam - Big thanks for your article. Learn a lot here.
A quick question: Is it possible to retrieve the IP addresses of the end users in the auditing implementation? If not, would you mind to share some possible workarounds to achieve that? It is for our customer's auditing needs and critical to the customer's consideration in it.
Appreciate your sharing.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hi,
Thanks for sharing this article.
I wanted to check if there is a table available which stores this information?
Or the only way to access this information is through API?
Ready to see what SAS Viya Copilot can do?
Visit the Tips & Tricks page for setup guidance, demos, and practical examples that show how Copilot supports your workflows.
SAS AI and Machine Learning Courses
The rapid growth of AI technologies is driving an AI skills gap and demand for AI talent. Ready to grow your AI literacy? SAS offers free ways to get started for beginners, business leaders, and analytics professionals of all skill levels. Your future self will thank you.
- Find more articles tagged with:
- Audit
- auditing
- authorization
- GEL
- Identities