- Home
- /
- SAS Communities Library
- /
- Auditing User Session Information in SAS Viya
- RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
Auditing User Session Information in SAS Viya
- Article History
- RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
Running a platform without auditing is a bit like playing sport with paying attention to the score (and please spare me the jokes about The Wallabies' efforts at the Rugby World Cup). The platform will run, but is it being used as intended, with the right people performing the right activities? How does it stack up in terms of efficiency and fitness for purpose? Auditing helps determine if the platform is running as expected and being used appropriately, or if there is anything that needs to be addressed before it becomes problematic. Are changes necessary to improve usability, performance, or security? Keeping an eye on things and taking preemptive action is good practice. SAS Viya 3.4's event-driven architecture offers the capability for effective auditing of system resources, report activity, data access, and more. In this post, we'll look at the options available for a fairly common auditing request; how can admins audit user access? How can we identify which users are logging in, how long they are staying logged in for, and at what times of the day?
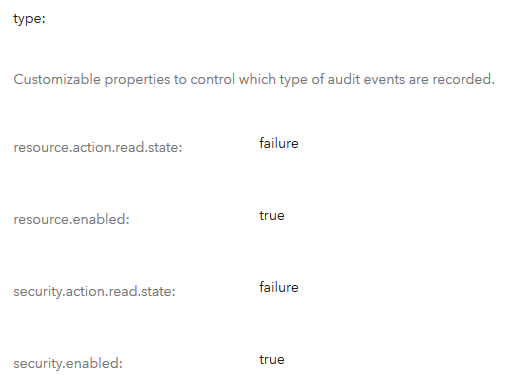
Information about logins and user sessions are captured in the security_audit tables in the AUDIT schema in the SAS Infrastructure Data Server. The default behaviour, as defined in the security type properties in the sas.audit.record configuration instance, is to capture read failures only on security actions.
 |
Select any image to see a larger version.
Mobile users: To view the images, select the "Full" version at the bottom of the page.
However, there is another event action more useful than read when trying to audit user login attempts; the login event, which will provide information about (successful and failed) login attempts coming from the SASLogon application. This information will be captured by default without the need to modify any of the default properties in sas.audit.record.
Let's look at an example. Below, we use the sas-admin CLI's audit plugin to see that user Ahmed logged in at 07:31 AM on the 25th of October (note that the timestamp is in UTC in PostgreSQL, but is converted to local time when a SAS Operations Infrastructure ETL job loads it to the AUDIT table in CAS).
/opt/sas/viya/home/bin/sas-admin --output text audit list --user-id Ahmed --sort-by ~timeStamp
ID Time Stamp Action State User ID Application URI
c72c4533-886d-493b-9ef2-1dcff4ff4674 2019-10-25T07:57:54.776Z SessionDestroyed success Ahmed SASLogon
bb748c54-6cb3-4edf-adbe-fce516c5786c 2019-10-25T07:31:21.014Z update success Ahmed reportImages /reportImages/jobs/4d7a64d8-1839-4d5b-a562-b140cdfc1f22/state
caf1264d-4d37-444b-af45-4e339edc5dc6 2019-10-25T07:31:20.999Z create success Ahmed reportRenderer /reportRenderer/images
713e18ac-34db-4115-92aa-35f7662b0909 2019-10-25T07:31:20.649Z read success Ahmed reportData /reportData/commons/settings
c5df6523-eb4f-42fe-b89b-fbdcc73d1c56 2019-10-25T07:31:20.298Z create success Ahmed reportPackages /reportPackages/jobs/b7325111-3f5a-4659-84bf-d1e59bdfbc74
e8578d9f-73b1-4dea-a94e-048a9eb9a72d 2019-10-25T07:31:20.030Z create success Ahmed reportData /reportData/jobs/61c55ce8-2b0a-4989-a14f-e1a5395b3b86
5aec043f-c2f8-46b6-a758-bc040abf1f69 2019-10-25T07:31:17.990Z create success Ahmed reportData /reportData/metadataSupplements
fc7c64d8-bf75-40f5-a851-4afa5dc29beb 2019-10-25T07:31:16.141Z create success Ahmed reportImages /reportImages/jobs/4d7a64d8-1839-4d5b-a562-b140cdfc1f22
f9ad69f9-22b8-447b-82c2-45ebeb462409 2019-10-25T07:31:14.523Z read success Ahmed reportData /reportData/commons/settings
5dc96422-833c-496c-bd65-64659faf76d0 2019-10-25T07:31:08.641Z read failure Ahmed preferences /preferences/preferences/@currentUser/FormatLocale.DefaultLocale
5da5acf5-4d6b-47b3-9da5-c30ea7c3d946 2019-10-25T07:31:08.096Z read failure Ahmed preferences /preferences/preferences/@currentUser/_hc_xx_
4a4c470f-afe9-469c-af3a-3fdb6d5f951e 2019-10-25T07:31:07.082Z read failure Ahmed preferences /preferences/preferences/@currentUser/FormatLocale.DefaultLocale
b66f6eed-8ae8-47a3-8d3a-60e23df5cec9 2019-10-25T07:31:05.463Z login success Ahmed SASLogon
When a user logs off Viya gracefully, a SessionDestroyed action is registered indicating the termination of the session as shown above.
If a user closes the browser instead of logging off, the SessionDestroyed does not get created in the audit records until the session times out. Session timeout is configurable by following instructions in Set Time-out Interval for SAS Viya Web Applications in SAS Viya 3.4 Administration: Configuration Pr....
Some applications generate their own audit data when a user logs in. For example, SASStudio V creates a Compute server session when a user logs in, and an audit record similar to the following is captured.
/opt/sas/viya/home/bin/sas-admin audit list --user-id Ahmed --sort-by ~timeStamp --details --application compsrv
ID Time Stamp Type Action State Description User ID Application Remote Address URI
1967127d-87da-4656-922f-ed3b3bf1733d 2019-10-23T11:47:42.122Z resource start success 92ce6360-b23c-485b-94dc-48e5bd681bdd:https://intviya02.race.sas.com:38934/compute/servers/92ce6360-b23c-485b-94dc-48e5bd681bdd Ahmed compsrv
When the compute session is terminated, an audit record from the compute application is captured indicating the deletion of the session (the Description field displays the ID of the session).
/opt/sas/viya/home/bin/sas-admin audit list --user-id Ahmed --sort-by ~timeStamp --details --application compute
ID Time Stamp Type Action State Description User ID Application Remote Address URI
5ebd10ca-b4e1-4e7e-b71d-2874bfa672ca 2019-10-23T07:50:36.257Z resource delete success Deleted compute server 92ce6360-b23c-485b-94dc-48e5bd681bdd Ahmed compute /compute/servers/92ce6360-b23c-485b-94dc-48e5bd681bdd
c9a1fc4a-48ea-4afa-a456-45e890571e42 2019-10-23T07:50:36.132Z resource delete success Deleted compute server session 92ce6360-b23c-485b-94dc-48e5bd681bdd-ses0000 Ahmed compute /compute/sessions/92ce6360-b23c-485b-94dc-48e5bd681bdd-ses0000
User sessions are assigned a unique session signature when they are established. The session signature (session_sig) property links the login event with the corresponding SessionDestroyed event. However, the session signature is not visible when surfacing audit records using the CLI. This information is recorded in TSV files in the EV Datamart directory (/opt/sas/viya/config/var/lib/evmsvrops/evdm/application/security) on the Viya server. When a session is started:
2 34dca2cc-fcc9-4b6d-8c72-32d2958c9320 security application/vnd.sas.event.security 2019-10-15T06:21:18.973000+00:00 sasadm sas-deployment-id:dml5YQ==,sas-event-source:U0FTTG9nb24=,session_sig:NTNlZmNlZGE= security action:bG9naW4=,actionState:U1VDQ0VTUw==
Note the session_sig value. When the session ends, another record will be generated in the same file, referring to the original signature (orig_session_sig) for that session.
2 b41e8882-192d-4657-8fee-4cb04a96abda security application/vnd.sas.event.security 2019-10-15T07:02:30.282000+00:00 sasadm orig_session_sig:NTNlZmNlZGE=,sas-deployment-id:dml5YQ==,sas-event-source:U0FTTG9nb24=,session_sig:NDk0MGZmNw== security action:U2Vzc2lvbkRlc3Ryb3llZA==,actionState:U1VDQ0VTUw==
Fortunately, the legwork for extracting this information has already been done. Session information is parsed from these files and stored in the authentications subject table (/opt/sas/viya/config/var/lib/evmsvrops/evdm/subjects/authentications.sas7bdat), providing a really nice way to audit user session information.
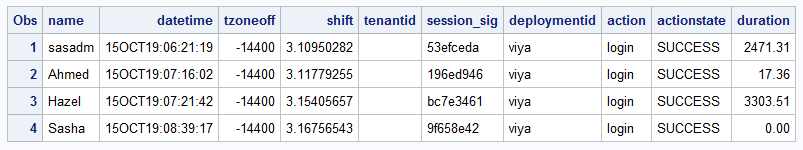
In the example below, several user sessions are listed, each with a datetime stamp of the login action, the session signature, and the duration of the session (in seconds ).
Note that user Sasha’s session has a duration of 0.00 seconds. This represents an active user session, indicating that Sasha has not yet logged out (SessionDestroyed action has not occurred for the session with this signature).
A job runs every 5 minutes to update this table, and another job runs daily to clear records older than 10 days.
We can query this table to get some more insights about user sessions. For example, a question to me posed recently was "How do I determine who was logged in at a certain time"?
A basic SAS program can be executed to answer that question.
/* Specify query time below in datetime. format */
%let qrytime='15OCT19:08:39:18'dt;
libname evdm '/opt/sas/viya/config/var/lib/evmsvrops/evdm/subjects' access=readonly;
data activesessions;
set evdm.authentications;
endtime=datetime+duration;
format datetime datetime.;
format endtime datetime.;
where &qrytime between datetime and &endtime or (&qrytime >= datetime and (duration=0 and session_sig ne '');
run;
proc print data=activesessions; run;
Note that this code sample is for demonstration purposes only, and there may be more efficient methods to extract the required user session information from the authentications subject table.
For more information on auditing in Viya, please refer to SAS Viya 3.4 Administration: Auditing.
Thank you for reading. I hope the information provided in this post has been helpful. Please leave a comment below to share your own experiences.
Catch up on SAS Innovate 2026
Nearly 200 sessions are now available on demand with the SAS Innovate Digital Pass.
Explore Now →SAS AI and Machine Learning Courses
The rapid growth of AI technologies is driving an AI skills gap and demand for AI talent. Ready to grow your AI literacy? SAS offers free ways to get started for beginners, business leaders, and analytics professionals of all skill levels. Your future self will thank you.